How to conduct a cybersecurity audit based on zero trust
The CISA Zero Trust Maturity Model is a framework for organizations in the public and private sectors that aims to increase efforts to prevent unauthorized access to technological infrastructure and information resources.
Developed by the US Department of Homeland Security’s Cybersecurity and Infrastructure Security Agency (CISA), the Zero Trust Maturity Model (ZTMM) is relatively new and is among many other similar maturity models dealing with cybersecurity.
Organizations will eventually need to conduct cybersecurity audits, especially as the CISA ZTMM and other Zero Trust frameworks gain traction, as organizations adopt Zero Trust methodologies and policies, and as government begins to mandate the use of Zero Trust.
Why zero trust cybersecurity readiness exams matter
Maintaining Zero Trust requires proactive management of policies and procedures. Failure to regularly review cybersecurity plans and procedures, and failure to regularly test these resources, can increase the risk of unauthorized cyberattacks.
Zero Trust compliance audits are an essential part of an organization’s efforts to adhere to Zero Trust models and related cybersecurity standards. They provide objective assurances that organizations have policies, procedures, trained personnel, trained employees, and supportive leaders in place. Audits also show that organizations have formal controls in place to ensure they are complying with policies and specifications. Finally, audits ensure that the IT infrastructure is functioning securely – and if not, they ensure that anomalies can be quickly identified and corrected.
Zero trust controls for audit investigations
The ZTMM document follows the seven baseline criteria of Zero Trust as defined in NIST Special Publication (SP) 800-207 (2020), Zero Trust Architecture, all of which can be viewed as controls in their own right. However, each control can be expanded into more detailed controls that address aspects of the baseline criteria.
For example, the third criterion says, “Access to individual corporate resources is granted on a session basis.” The following are supplemental controls that can support the baseline control as part of an audit investigation:
- Access to organization resources is defined by a policy.
- Access to organizational resources is governed by a number of procedures.
- Access to all resources is based on the need of an individual employee.
- Access to resources is based on an employee’s role in the organization.
- Access to resources is granted on a per-session basis, based on the employee’s role and knowledge needs.
- Termination of a session terminates further access to resources unless a new session is initiated.
- Access to resources is granted through a multi-step process that includes a user ID and multi-factor authentication (MFA).
- No more than three unsuccessful access attempts should be made before access is denied and must be restored by a security administrator.
- User access passwords must be updated every 60 days.
- User authentication methods must be reviewed every six months and updated as necessary.
Best practices for preparing for zero trust audits
The most important elements of exam preparation are the overall preparation and documentation. These steps include the following:
- Secure management approval and audit funding.
- Set up an review team to interact with reviewers.
- Evaluate the examiners’ skills and experience in examining cybersecurity issues.
- Understand the zero trust model.
- Understand relevant cybersecurity standards and best practices.
- Prepare an exam plan.
- Secure printed and electronic evidence, including policies and procedures; cyber security plans; Screenshots of various cyber security features; Records of various activities, such as B. Patching and updating firewall rules; and system test reports.
- Provide copies of previous assessments, audits and other analytical reports.
- Provision of a workspace for auditors.
Audit Checklist for the CISA Zero Trust Maturity Model
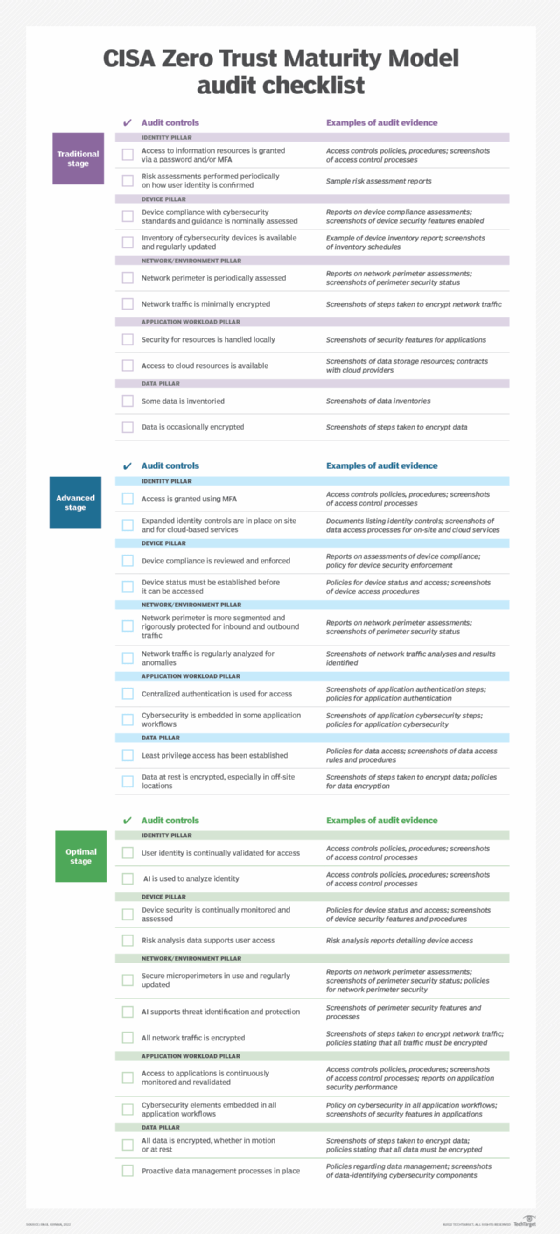
The ZTMM document details activities that can be addressed as organizations evolve their Zero Trust capabilities through three specific phases—traditional, advanced, and optimal—using five pillars of Zero Trust development: identity, device, Network/Environment, Application Workload and Data.
The following checklist provides a general overview of proposed audit controls and examples of evidence based on the ZTMM. The three steps and five pillars are built into the table.
Download a copy of the CISA ZTMM Checklist here.